It's 2:17 AM. A 280 Gbps volumetric flood just hit your network. Your upstream provider's automated systems kick in, and within minutes, your customer traffic is being diverted to a scrubbing center in Frankfurt. You're based in São Paulo.
The attack gets mitigated. Your customers stay online. Everything works as designed. But here's what nobody talks about in the post-incident review: that diversion just cost you $14,000 in transit fees, added 180ms of latency to every customer session for 45 minutes, and degraded the experience for 30,000 subscribers who weren't even targeted by the attack.
For ISPs managing DDoS protection cost reduction, the math is straightforward — every offshore diversion is money out the door.
The hidden cost of cloud-only DDoS mitigation
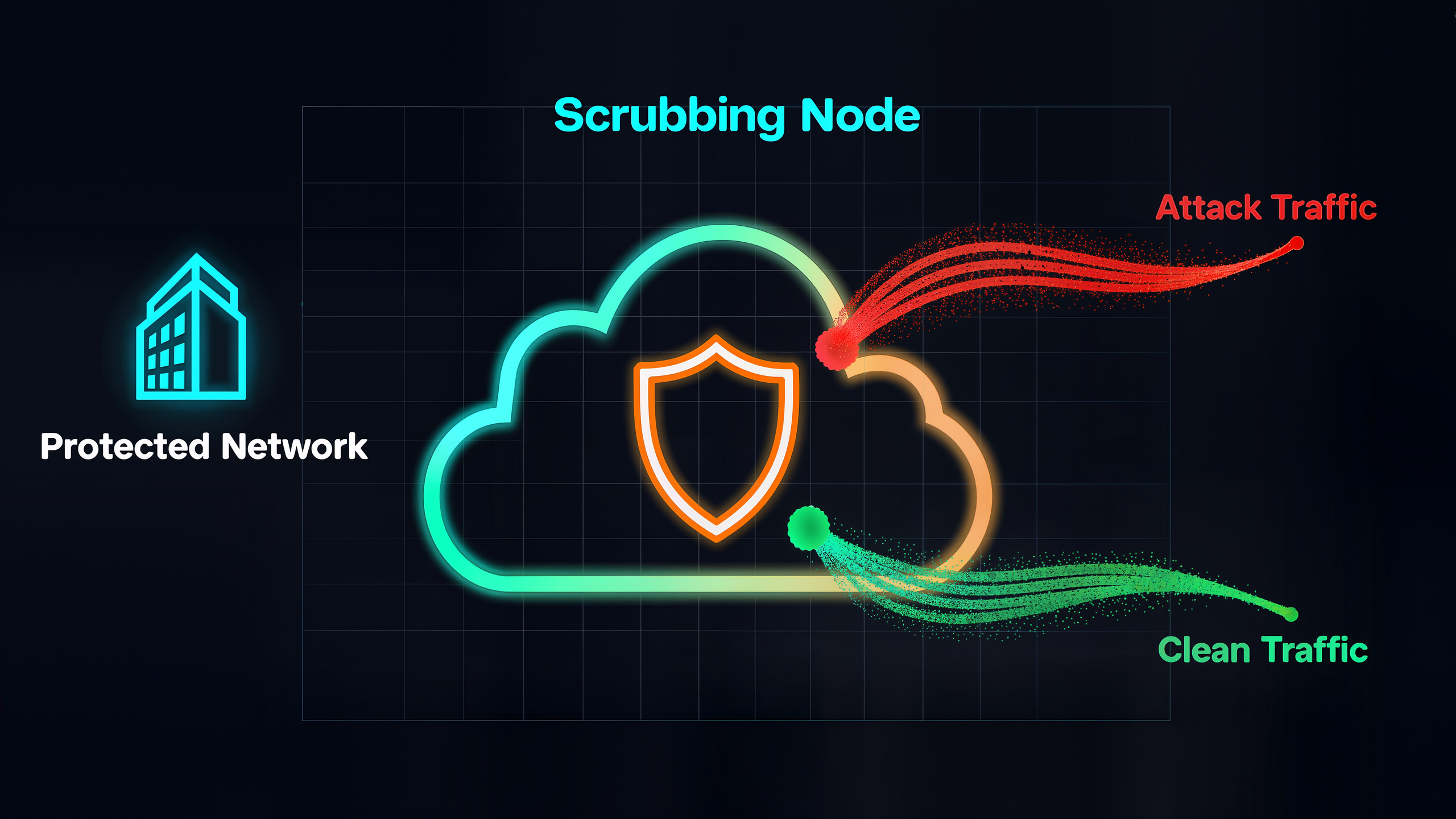
Most ISPs rely on cloud-based scrubbing as their primary DDoS defense. The model is straightforward: when an attack is detected, BGP reroutes traffic to the nearest scrubbing center, malicious packets are filtered, and clean traffic returns via GRE tunnel. It works. But "works" and "works efficiently" are very different conversations when you're running the numbers at the end of the quarter.
The fundamental problem is geographic. If your subscribers are in Latin America, Southeast Asia, or Central Europe, the nearest scrubbing center may be thousands of miles away. Every diversion means transit costs, latency spikes, and a degraded experience for your entire customer base — not just the targeted IPs.

Why local scrubbing changes the economics
Nexusguard's true-hybrid approach deploys on-premise Bastions servers that handle the first line of defense locally. Small and medium attacks — the ones that make up 85% of DDoS incidents — are scrubbed at the edge, inside your network, with zero transit cost and zero added latency. Only massive attacks that exceed local capacity get escalated to the cloud scrubbing network.
The result: your routine DDoS mitigation costs drop dramatically because you're not paying international transit fees for every 5 Gbps nuisance attack. Your customers experience zero latency impact for the vast majority of incidents. And when a truly large attack hits, you still have the full cloud network as overflow capacity.
What this means for your bottom line
For a mid-size ISP handling 10-15 DDoS events per month (which is conservative — Nexusguard's 2025 threat report shows attacks doubling year over year), the difference between routing everything offshore and scrubbing locally can be six figures annually in transit savings alone. Factor in the customer experience improvement and reduced churn from latency-sensitive subscribers, and the ROI case becomes overwhelming.

FAQ
Q: What is hybrid DDoS mitigation?
A: Hybrid DDoS mitigation combines on-premise scrubbing hardware (deployed in your data center) with cloud-based scrubbing capacity. Local attacks are handled on-site with zero latency impact, while large-scale attacks overflow to the cloud network. This approach is central to ISP DDoS protection cost reduction because it eliminates transit fees for routine attacks.
Q: How much does local DDoS scrubbing save versus cloud-only?
A: Savings depend on your traffic volume and geographic location, but ISPs typically see 40-60% reduction in DDoS-related transit costs by handling routine attacks locally instead of diverting all traffic to distant scrubbing centers.
Q: What is Nexusguard Bastions?
A: Nexusguard Bastions is a purpose-built on-premise DDoS mitigation server that integrates with Nexusguard's global cloud scrubbing network. It provides always-on local detection and mitigation while maintaining cloud overflow capacity for large-scale attacks.


